Infra Play 137: Okta
The identity security company that outsourced its identity
Acquiring CyberArk is the conviction play that will define Nikesh’s tenure at PANW. The core thesis is that Privileged Access Management (PAM) is the essential vector of attack in the majority of breaches (as stated in the Unit 42 research report) and CyberArk was the market-leading solution in its category. As agents start being more embedded in IT, and specifically in admin roles with extended privileges, PAM, together with strong AI observability (i.e. Chronosphere), becomes the most important security battleground.
This sounds good, until you realize that CrowdStrike already had a $450M+ ARR identity business and has been building out as what they pitch the next evolution of PAM, focused on dynamic, just-in-time access driven by real-time endpoint and AI signals.
In my deep dive on Palo Alto Networks, I covered the importance of the CyberArk acquisition extensively and how it relates to the platform plays for both PANW and CrowdStrike.
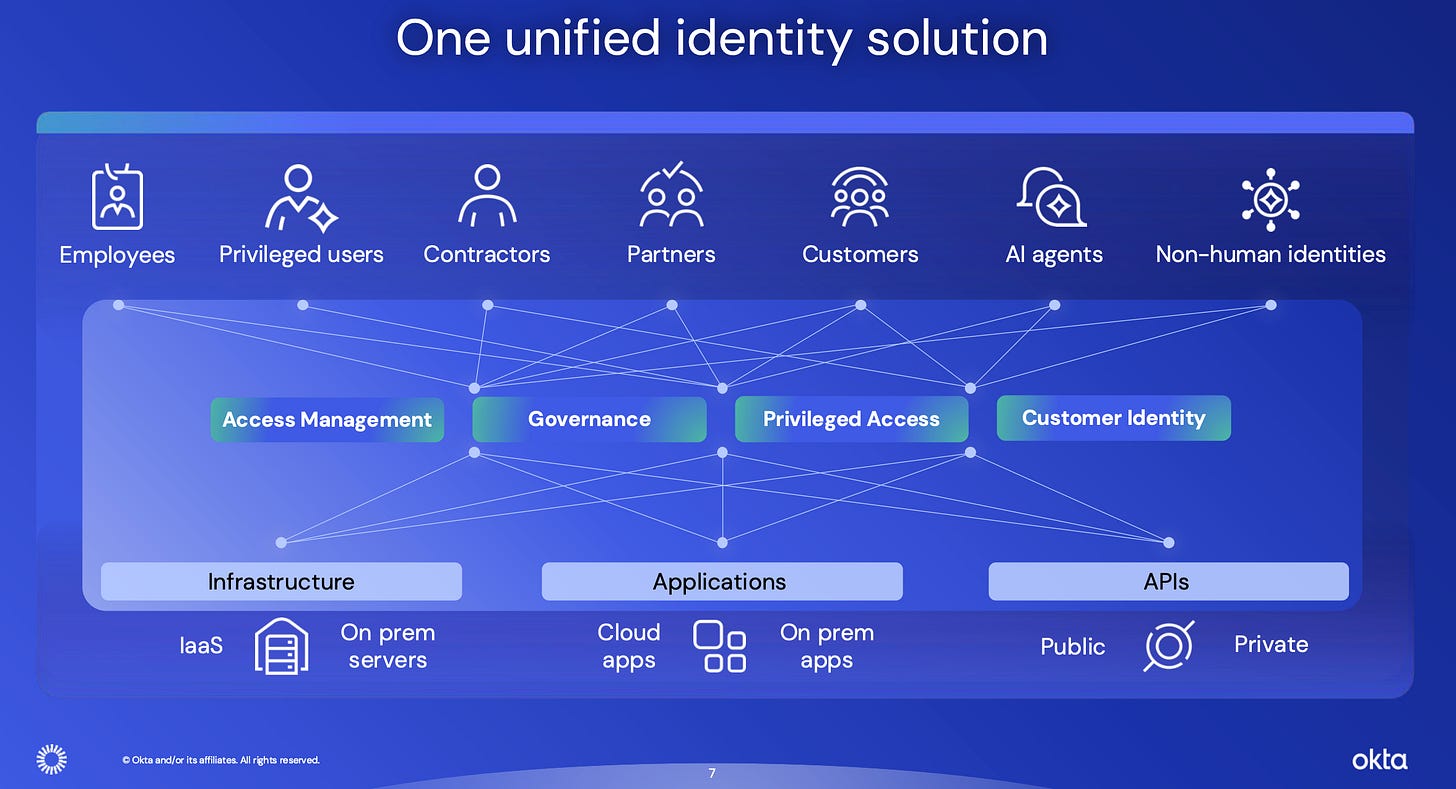
Identity is a peculiar market because it has several important elements:
It’s essentially mandatory in order to drive improved security outcomes vs. the alternatives.
It has a massive tailwind coming from the explosion of AI agents needing to authenticate themselves as they start interacting with existing enterprise environments.
Identity has a productivity benefit (access all applications with a single login), with security outcomes being a byproduct.
On paper, there is no reason AI is not driving a massive business opportunity for Okta.
Similar to Atlassian, this is also a company still founder-led and sitting in the middle of a significant jump in relevant workloads for their core products. Todd even likes to talk about what a big focus GTM is for him!
Last week was our FY27 Company and Sales Kickoffs. The energy was high, and the focus was clear: Okta secures AI. Congratulations to our Founder’s Award winners. You represent the best of our culture. Let’s go, FY27!
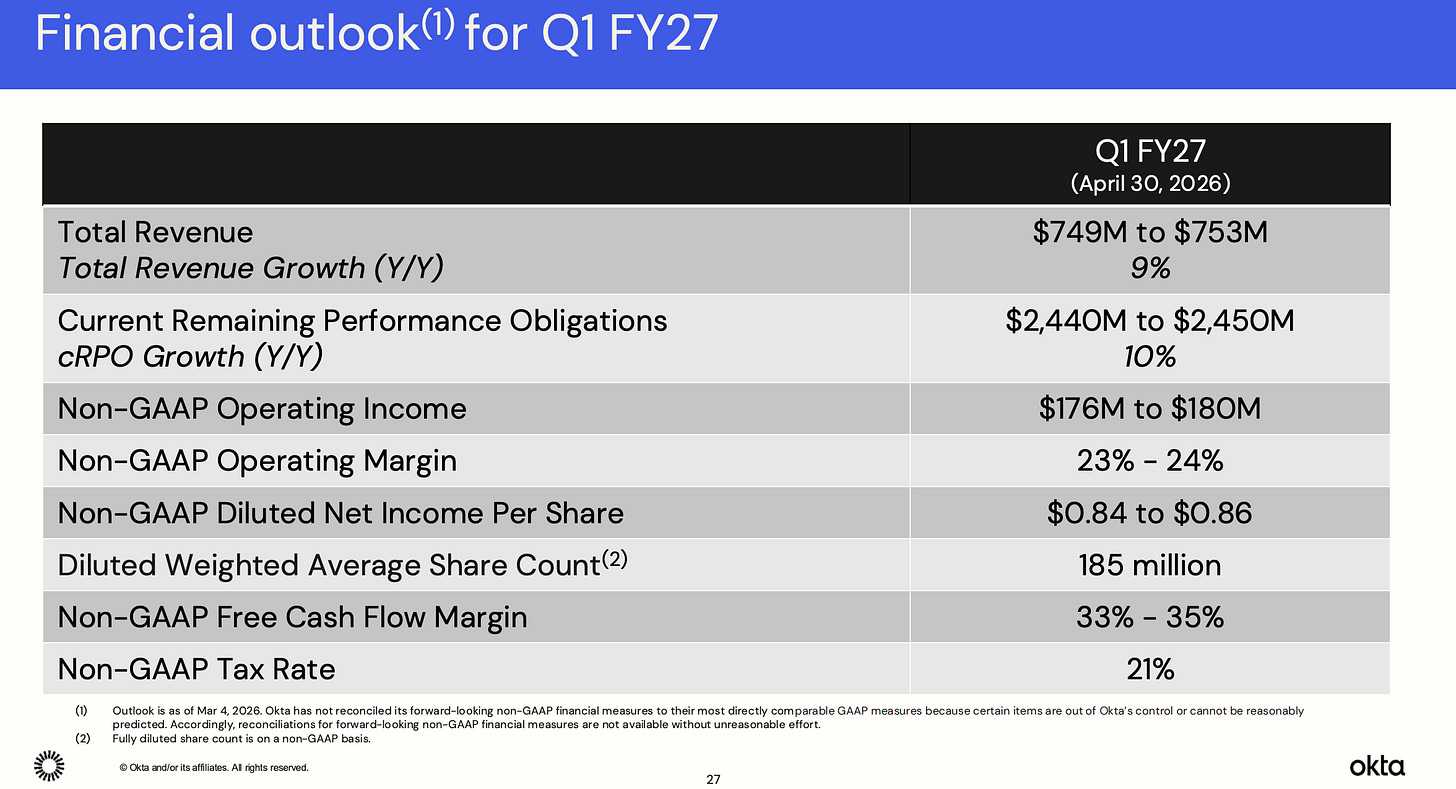
Yet, we are looking at 9% growth in the next twelve months. What’s going on here?
The key takeaway
For tech sales and industry operators: Okta's business model rests entirely on switching costs. The only question that matters is whether those costs are rising or falling as agentic AI restructures enterprise IT. The reality of a business with a continuously declining net retention rate is that it is running hard to stand still, and any further deterioration in that number reveals just how thin the actual moat is. The plan for the next twelve months is that Okta will stop offering services and outsource implementation to GSIs. This means they have given up on building proprietary knowledge about how customers actually deploy and use their products, and that proprietary deployment knowledge is precisely what would give them an unfair advantage in an agentic world where configuration complexity is exploding. The deepest problem with Okta is not the low growth rate but that nobody on the leadership team can articulate what they know about the future of identity that nobody else does. The current vision from the CEO is that the market hasn't standardized, there is no consensus on the AI security stack, and that Okta will somehow win the default role of identity management anyway. Don't commit your career capital and valuable years in the middle of a massive tech transformation to this bet.
For investors and founders: The management team is telling the same story about being a neutral platform for the last five years. Their view is that identity security for agentic AI is additive, not transformative. This is a direct consequence of Okta having chosen breadth over depth in every new product decision: OIG competes with SailPoint, PAM competes with CyberArk, AI agents compete with nobody and everybody. That is the portfolio strategy of a company that has lost conviction in its core differentiation. The contrarian take is that Okta will likely get acquired within three years by a company that needs its install base (Microsoft, Salesforce, or a large systems integrator) at a modest premium to where it trades today, with the upside from the agentic thesis going to the acquirer rather than current shareholders. If you want exposure to securing agentic identities, the better bet is a well funded private company with a single, deep technical insight about how agents authenticate (WorkOS, cough, cough). Not a public company retrofitting a human identity platform to serve a fundamentally different use case, while others are reimagining this problem as an embeddable infrastructure inside your product.
Low growth identity
Todd McKinnon: In today's call, I'll cover the success we're having with our new products, how Okta secures AI, including some early success we're having in that new market and close with our top priorities for FY '27. We continue to see strong performance from our portfolio of new products. This group consists of Okta Identity Governance, Okta Privileged Access, Identity Security Posture Management, Identity Threat Protection, Okta Device Access and Fine-Grained Authorization.
And new to this group are our products, Auth0 for AI Agents and Okta for AI Agents. The value of a unified identity system with a single control plane is resonating with customers. In aggregate, these new products represented approximately 30% of Q4 bookings, which is a meaningful increase from prior quarters. And when these new products are included in a deal, the average contract uplift is approximately 40%.
Okta Identity Governance continues to be the biggest of these new products and is building on its early success. OIG now has over 2,000 customers. That's remarkable progress in just over 3 years and it underscores the market demand for a modern governance solution. Customers are choosing OIG because it's a full IGA cloud-native solution built into our unified platform, not a siloed point solution.
I mentioned that our portfolio of new products now includes our AI products, Auth0 for AI Agents and Okta for AI Agents. It's still early for this developing market, but as the leading modern identity solution for workforce and customer identity, Okta is uniquely positioned to help organizations combat the growing security threat that AI agents represent. The reality is that the AI revolution has moved faster than today's security frameworks.
According to Okta's AI at Work report, 91% of surveyed organizations are already using AI agents, but only 10% have a governance strategy in place. In meetings that I've had with customers and prospects over the past 6 months, the vast majority of the conversations revolve around their AI initiatives and how Okta can help them build and manage agents securely.
As AI becomes embedded in more workflows and automations, the growing number of exploitable entry points from nonhuman identities to unsecured integrations expand the attack surface for threat actors. It's clear that in order to get AI right, you have to get identity right. Okta was built to meet this challenge. Identity isn't just a feature for us. It's our foundation. AI agents are simply a new identity type and protecting them is a natural extension of what we do best.
Okta's neutral and independent identity solution is uniquely positioned to secure and govern the entire agentic life cycle and gives customers the freedom to deploy on any agent platform without ecosystem lock-in, all while strengthening their security posture. Our two-pronged solution with Auth0 and Okta for AI Agents treats AI agents with the same importance as humans and gives customers everything they need to secure this powerful new technology.
We're still in the early stages, but we believe that in a few years, agents and agentic systems won't be the exception to how enterprise software is built and operated. They'll be the rule. We believe that AI agents represent nothing less than the future of software. That's why AI security is identity security. I'd like to highlight a couple of AI deals we closed in Q4 that illustrate how we're addressing the AI market.
The problem with the agentic narrative for identity security is that it's directionally correct, but the workloads are obviously not there yet. While enterprises are deploying a lot of compute across a variety of agents, those are typically used within the closed ecosystem of a specific tool. Claude Code, the coding agent, doesn't need a special Okta license to produce code. Agentforce agents don't require Okta access for the majority of interactions. An internal application that can simply be secured by existing user logins doesn't require a special Okta agent license.
Todd McKinnon: An existing Auth0 customer is building AI agents as part of their leading financial services platform. These agents will help the firm’s advisers make better and faster decisions. But to do so, the agents need access to sensitive customer information, which must be least privileged, and they need to work with existing systems and third-party services inside the financial institution. The customer picked Auth0 for AI Agents as it met their stringent requirements for a secure, extensible platform to build and deploy agentic systems.
They needed a solution that offered enterprise-grade identity for humans and agents while providing secure access to third-party MCP servers, all while acting as a single source of truth. Another notable deal that included Okta for AI Agents, which became available in early access in January was with a top global business and technology services provider.
They chose Okta for AI Agents to help them discover, control and govern identities for their growing sprawl of agents. Rolling out AI agents across multiple agent platforms is key to their ongoing transformation and centralizing agentic identities in an independent agent-agnostic platform like Okta will strengthen their cybersecurity posture. This is the very beginning of the AI opportunity.
Now, tracking the deployment and usage of AI agents is a different play, and it comes back to the idea that the best security business comes as a byproduct of productivity benefits. Helping IT understand the scope of usage and track it in a single overview can be very beneficial, with the side benefit of controlling what those agents can access. The challenge with this approach is that:
ITSM companies like ServiceNow have a more logical entry into winning those workloads.
Most agents are currently easy to control since they live in one or two applications.
Todd McKinnon: And finally, I always like to take time on the Q4 call to share our priorities for the new fiscal year. It shouldn’t be surprising that all of these priorities are focused on driving growth.
The first priority is Okta Secure AI, which is all about how we win, grow and become the standard for securing agentic AI.
By building on our early success with Okta and Auth0 for AI Agents, we will further our vision of freeing everyone to safely use any technology. The second priority is increasing our focus on landing bigger and growing faster with large customers. We want these organizations to think of Okta first when it comes to identity security and securing AI. This is a global effort across both the Okta and Auth0 platforms.
And our third priority is becoming the default identity security solution for the U.S. federal vertical and highly regulated industries. The public sector has been one of our fastest-growing verticals over the past couple of years, but we’ve only begun to scratch the surface of the overall opportunity. To wrap things up, we’re pleased with the strong finish to FY ‘26. We’re excited about the momentum we’ve built for the year ahead as we look to surpass $3 billion in revenue on our way to $5 billion and then $10 billion.
Identity is security, and we’re building on our position as the leading modern identity solution to win the emerging market for securing AI. It’s an exciting opportunity, and we’re going after it aggressively. I want to thank the entire Okta team for their tireless effort and also thank our loyal customers and partners who put their trust in us every day.
So Okta's big pivot this year focuses on three plays. First, agentic security; a relevant topic but clearly lagging in revenue potential in the short term. Second, "do big deals," as if nobody has thought about that before. Last, try to sell to the Feds, who are signing large frameworks with a number of vendors that already have a play in identity rollouts.
All of this effort will result in maybe 9% growth over the next twelve months. I’m shocked investors aren’t lining up to buy the stock.